Nodemailer imitator nodejs-smtp clips Atomic and Exodus wallets
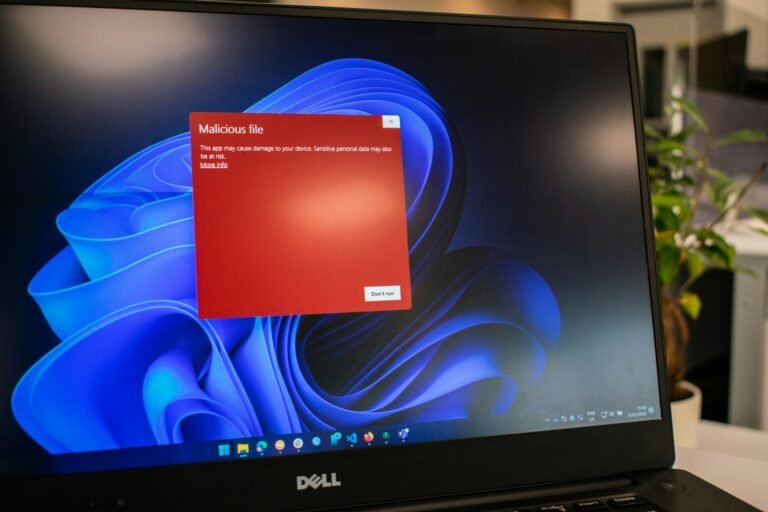
Cybersecurity researchers have uncovered a malicious npm package named Nodejs-Smtp, which stealthily injects harmful code into desktop applications for cryptocurrency wallets such as Atomic and Exodus on Windows systems. This package, uploaded in April 2025 by a user named “nikotimon,” impersonates the legitimate email library Nodemailer, featuring identical taglines, page styling, and README descriptions. Despite attracting 347 downloads, it is no longer available. Upon import, the package utilises Electron tooling to unpack Atomic Wallet’s app.asar, replace a vendor bundle with a malicious payload, and repackage the application while erasing traces by deleting its working directory. The primary aim is to overwrite recipient addresses with hard-coded wallets controlled by the threat actor, redirecting transactions of Bitcoin (BTC), Ethereum (ETH), Tether (USDT and TRX USDT), XRP (XRP), and Solana (SOL), effectively functioning as a cryptocurrency clipper.
The Nodejs-Smtp package maintains its stated functionality as an SMTP-based mailer, which helps to avoid raising developers’ suspicions. It exposes a drop-in interface compatible with Nodemailer, allowing application tests to pass and giving developers little reason to question the dependency. This discovery follows a similar incident where ReversingLabs identified another npm package, “Pdf-To-Office,” which achieved the same malicious goals by modifying JavaScript files within the app.asar archives of Atomic and Exodus wallets. Kirill Boychenko, a researcher at Socket, highlighted that this campaign demonstrates how a routine import on a developer workstation can discreetly alter a separate desktop application and persist across reboots. By exploiting import time execution and Electron packaging, a lookalike mailer transforms into a wallet drainer, compromising Atomic and Exodus on affected Windows systems.