My Courses
-

Docker vulnerability (CVE-2025-9074) allows container escape, assigned CVSS of 9.3
Docker has released critical fixes for a significant security vulnerability affecting the Docker Desktop application for Windows and macOS. This flaw, identified as CVE-2025-9074, has…
-

Phishing Attack Employs UpCrypter in Fraudulent Voicemail Emails to Distribute RAT Payloads.
Cybersecurity researchers have identified a new phishing campaign that employs fake voicemails and purchase orders to distribute a malware loader known as UpCrypter. The campaign…
-
Transparent Tribe spear-phishing Indian government using weaponised desktop shortcuts
The advanced persistent threat (APT) actor known as Transparent Tribe has been observed targeting both Windows and BOSS (Bharat Operating System Solutions) Linux systems with…
-

Reasons Behind SIEM Rule Failures and Solutions: Lessons Learned from 160 Million Attack Simulations
Security Information and Event Management (SIEM) systems serve as essential tools for detecting suspicious activities within enterprise networks, enabling organisations to identify and respond to…
-
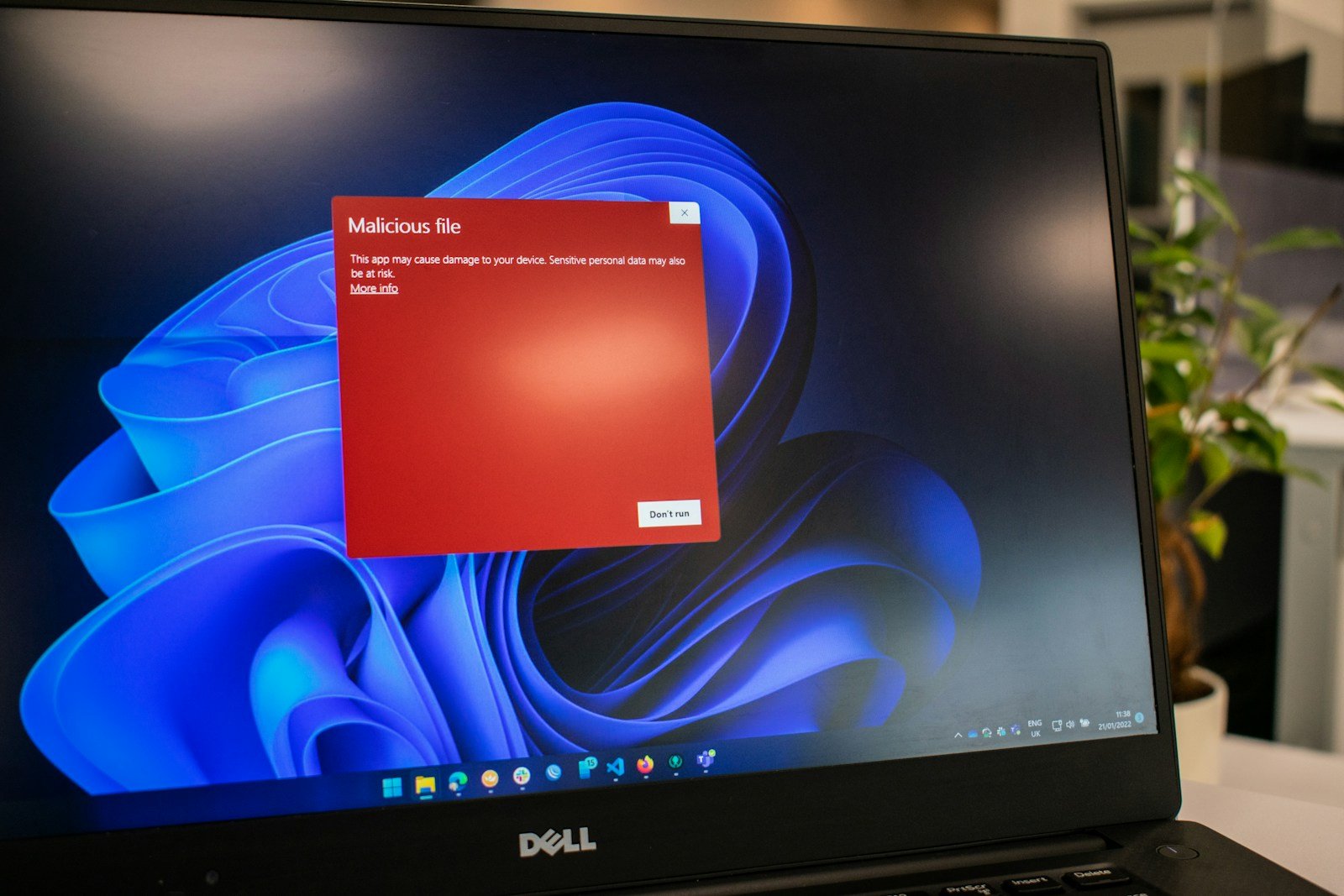
Is an SSH brute-force Go module stealing your credentials?
Cybersecurity researchers have identified a malicious Go module, dubbed “golang-random-ip-ssh-bruteforce,” which masquerades as a brute-force tool for SSH but is designed to covertly exfiltrate credentials…
-
Robust MLSecOps vital for managing vulnerabilities
Organisations that fail to adapt their security programs while implementing Artificial Intelligence (AI) risk exposure to a range of both traditional and emerging threats. MLSecOps…
-

Lightweight LLMs decrease incident response time using decision theoretic planning
Researchers from the University of Melbourne and Imperial College London have developed a novel method for enhancing incident response planning using Large Language Models (LLMs),…